VPNの仕組みを理解する:トンネリングと暗号化の基礎
VPNがどのように機能するのかを、技術的な正確さを保ちながら初心者向けに説明します。暗号化、トンネリング、プロトコルについて学びましょう。

VPNを有効にした瞬間、あなたのインターネット通信は一体どこに行ってしまうのでしょうか。ウェブサイトを閲覧するとき、メールを送るとき、動画をストリーミングするとき、あなたのデバイスから送られるデータはいくつもの段階を経て目的地に到達します。VPNはその経路を根本的に変えます。この記事では、VPNスイッチを入れたときに実際に何が起こるのか、そしてなぜそれが重要なのかを、マーケティングの装飾なしで説明します。
VPNなしでは、あなたのインターネットプロバイダ(ISP)があなたのすべての通信を見ることができます
VPNについて理解するには、まず通常のインターネット通信がどのように機能するかを知る必要があります。あなたがウェブサイトにアクセスするとき、あなたのデバイスはそのウェブサイトのサーバーにリクエストを送信します。このリクエストには、あなたのIPアドレス(インターネット上の住所のようなもの)が含まれています。ウェブサイト、あなたが訪問しているドメイン、送受信するデータの内容—ISPはこれらすべてを見ることができます。これは、あなたが郵便局を通じて手紙を送るとき、郵便局の職員があなたが誰に何を送っているかを知る可能性があるようなものです。
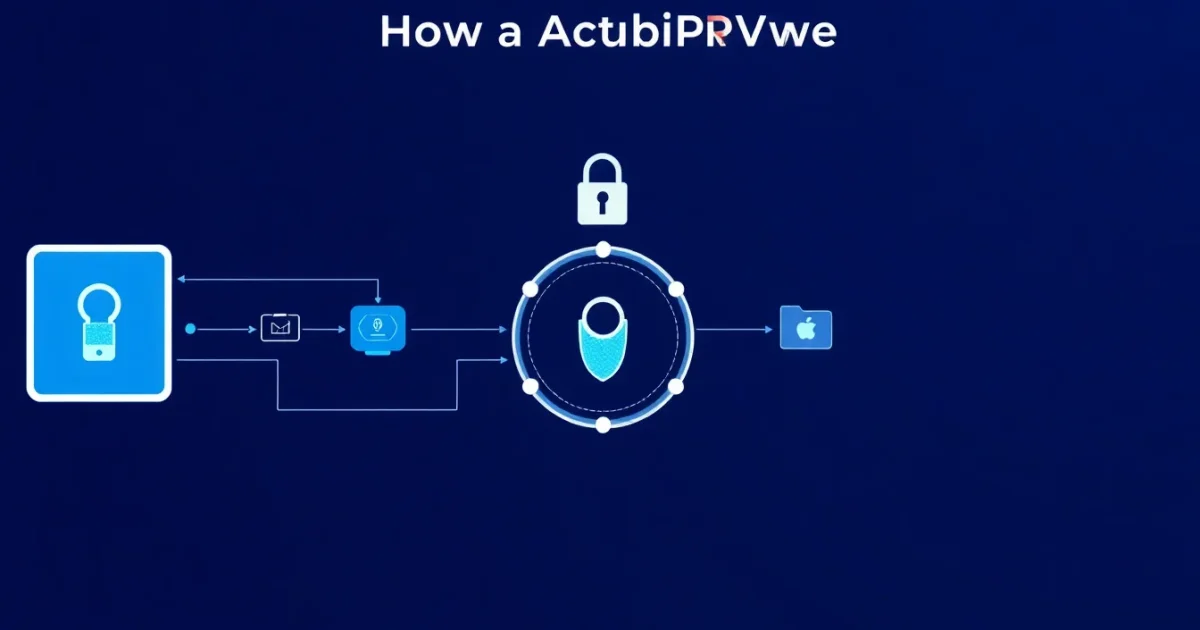
VPNは、あなたのデバイスとVPNサーバーの間に暗号化された専用経路を作成します
VPNの核心は「暗号化トンネル」という考え方です。VPNクライアント(あなたのデバイスにインストールするアプリケーション)を起動すると、最初にやることはVPNサーバーとの接続を確立することです。このプロセスは、二人の人物が初めて出会うときに、秘密の合言葉やサインを確認するようなものです。クライアントとサーバーは、すべての通信を暗号化するために使用する鍵を交換します。この鍵交換のプロセス自体も暗号化されているため、第三者がこのプロセスを観察していても、その鍵が何であるかは分かりません。接続が確立されると、トンネルが形成されます。これは、あなたのすべてのインターネットトラフィック(ウェブリクエスト、メール、動画ストリーミング、あらゆるものです)がこのトンネルを通って流れることを意味します。
カプセル化とは、あなたのデータを二重に包装することです
あなたのデータがこのトンネルを通るとき、何か興味深いことが起こります。それは「カプセル化」と呼ばれるプロセスです。例えば、あなたがウェブサイトにリクエストを送信するとします。このリクエストには、すでに宛先アドレスが含まれています。VPNがこのリクエストを取り、それを暗号化し、VPNサーバーの宛先住所を付けた新しい封筒に入れるようなものです。外から見ると、データはVPNサーバーに向かっているように見えます。あなたのISPや他の観察者は、元のリクエストが何であったか、どこに向かっているのかを見ることはできません。なぜなら、本来のデータはすべて暗号化されているからです。これは、封筒の中に別の封筒を入れて郵便で送るようなものです。郵便局は外側の封筒だけを見ることができ、内側に何があるかは知りません。
VPNサーバーはあなたの代わりにリクエストを転送し、レスポンスを返します
VPNサーバーにデータが到着すると、サーバーはそれを復号化します。つまり、暗号化を解除して、元のリクエストを読むことができるようにします。その後、サーバーはそのリクエストをあたかも自分自身から来たかのように、最終的な目的地(例えば、あなたがアクセスしようとしているウェブサイト)に転送します。ウェブサイトのサーバーは、リクエストがあなたから来たのではなく、VPNサーバーから来たように見えます。ウェブサイトはあなたの実際のIPアドレスを見ません。代わりに、VPNサーバーのIPアドレスを見ます。ウェブサイトがレスポンスを送信するとき、それはVPNサーバーに返されます。VPNサーバーはそのレスポンスを再度暗号化し、あなたのデバイスに送り返します。あなたのデバイスは暗号化を解除し、ウェブページを表示できるようになります。
一般的なVPNプロトコルは異なるアプローチを取ります

VPNトンネルを作成する方法はいくつかあり、異なるプロトコル(通信ルールのセット)を使用します。WireGuardは比較的新しいプロトコルで、シンプルさとスピードで知られています。OpenVPNはより古く、より多くの設定オプションを提供します。IKEv2はモバイルデバイスで特に有用です。これらのプロトコルは基本的な原則—接続確立、暗号化、カプセル化—に従いますが、詳細はそれぞれ異なります。どのプロトコルが「最高」かは、用途、デバイス、そしてあなたが何を最優先するかに依存します。これは「最高のハンマー」が存在しないように、「最高のプロトコル」も存在しません。
VPNプロバイダが見ることができることと、できないことを理解することが重要です
VPNはあなたのISPからデータを隠しますが、完全な匿名性を提供しません。VPNプロバイダ自身はあなたのトラフィックを見ることができます。彼らは、どのウェブサイトを訪問し、どのサーバーと通信しているかを知っています。ただし、通常、彼らはあなたの暗号化されたデータの内容は見ることができません。このため、VPNプロバイダを選ぶときは、彼らのプライバシーポリシーを理解することが重要です。また、VPNを使用していても、あなたがウェブサイトにログインすれば、ウェブサイトはあなたが誰であるかを知ります。VPNはあなたのIPアドレスを隠すだけです。
VPNの基本を理解することは、より大きなインターネットセキュリティの絵を見るための基盤です。あなたが今学んだことは、トラッフィック分析、端末暗号化、プロキシサーバーなど、他のプライバシーツールを理解するために必要な概念です。すべてのテクノロジーにはトレードオフがあります—VPNはあなたのISPからは隠しますが、別の信頼できるエンティティ(VPNプロバイダ)が必要になります。それが機能するかどうかは、あなたの状況と脅威モデルによって異なります。
おすすめVPNサービス
世界中で信頼される厳選VPN
※ save-clipは当サイトのリンク経由でご登録いただいた場合に手数料を受け取ることがあります。これによりツールを無料で提供し続けることができています。